While 2020 could justifiably be dubbed “The Year of the Banking App,” the picture isn’t all rosy. And the trend brings with it increased obligations for financial institutions to maintain close control of their app development and maintenance and to help consumers protect themselves.
Installations of financial apps on mobile devices rose by 15% in 2020 as more consumers needed remote means of handling their banking, as tracked in a study by Liftoff and App Annie. Globally, people installed 4.6 billion financial apps and spent 16.3 billion hours using them, the latter an increase of 45% over 2019.
It was a phenomenal year for the mobile banking app, as all those users downloaded and explored these programs, many for the first time. With that growth comes a significant caveat:
What many new and experienced users likely didn’t know was that they may also have been downloading multiple kinds of exposure to hackers and others who can exploit vulnerabilities in app components.
The Synopsys Cybersecurity Research Center evaluated over 3,000 of the most popular Android apps as ranked on Google Play, including 107 banking apps. The apps came from all over the world. The analysis was conducted using its Black Duck security software, designed to detect vulnerabilities.

Unlocking Digital Acquisition: A Bank’s Journey to Become Digital-First
This webinar will offer a comprehensive roadmap for digital marketing success, from building foundational capabilities and structures and forging strategic partnerships, to assembling the right team.
Read More about Unlocking Digital Acquisition: A Bank’s Journey to Become Digital-First

Send the Right Offers to the Right Consumers
Achieve a better return on your marketing investment. Leverage behavioral data and analytics to target the right customers with the best possible offers.
Read More about Send the Right Offers to the Right Consumers
Nearly Nine in Ten Have Potential Problems
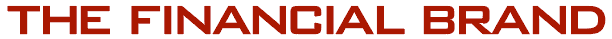
Of the 107 banking apps, 88% contained some form of known vulnerability, versus an average among all app categories of 63%. On average, banking apps contained 55 vulnerabilities each. “Financial applications require some of the most personally sensitive data, making these numbers alarming due to the potential impact of a security breach,” states the firm’s report.
Indeed, banking apps — including those from banks, fintechs and related types of companies — showed the third-highest level of potential exposure to loss of personal information or other infiltration, according to the firm’s analysis. Only two categories of game apps came ahead of banking apps, which was followed immediately by budgeting and payment apps.
The analysis looked for three major areas of potential app exposure:
- Security vulnerabilities in “open source” software widely used by app developers. The analysis found that 98% of the thousands of apps scanned contain some open source software. This is software that can be publicly licensed and incorporated into other programs, such as apps.
- Potential cases of information leakage resulting from app developers inadvertently leaving sensitive data such as passwords or keys exposed in the apps as released.
- Mobile permissions — when an app asks the user to allow it to tap various mobile device functions like a camera or location services — that may go beyond what’s needed or that may expose personal data to compromise.
“For consumers, this report highlights the jarring reality that even the most popular mobile apps are not immune to security and privacy weaknesses and should not be trusted implicitly. For app developers, this underscores the urgent need for secure software development practices and better overall privacy and security hygiene.”
— from “Peril in a Pandemic: The State of Mobile Application Security”
This contrasts with the blithe way most people download apps for all sorts of reasons with little thought of any possible consequences. Synopsys evaluated Android apps because they can be downloaded in a way that permits analysis piece by piece and end to end, according to Tim Mackey, Principal Security Strategist. Apps downloaded from the Apple Store are encrypted and can’t be analyzed in that way, he explains, though vulnerabilities can be similar.
Read More: How the Best in Banking Are Marketing Their Mobile Apps
Understanding the Sources of Banking App Vulnerabilities
The potential exposure banking apps face does not imply that major leakages are occurring, only that they could occur, especially if financial services providers and consumers don’t observe appropriate caution and best practices.
The risk is out there. In its March 2021 quarterly fraud report, RSA Security reported that across the web, mobile browser and mobile app, the apps accounted for 44% of frauds in the fourth quarter of 2020, the largest share, in the wake of growing use of apps during the pandemic. (RSA figures include rogue app fraud, when criminals publish phony apps to fool people into loading them. They can then steal credit card and other sensitive data.)
To illustrate how many of the risks arise, in an interview with The Financial Brand, Mackey explains that the days are long gone when everything in a software package was developed entirely by the organization releasing the final product.
“There’s more of a supply chain effect today,” explains Mackey. “Components are coming from libraries of code that are authored by somebody else or even a group of somebody elses.” Typically these libraries are built on open-source software, which is licensed and which typically has vulnerabilities that get fixed as they are discovered.
“You don’t want someone reinventing the wheel any more than you have to,” Mackey continues. “When it comes to things related to security, you’re not going to find the average software developer very well-versed on things like cryptography and encryption. They’re going to use a third-party library produced by a team that understands security really well. And, software being software, they make mistakes from time to time and so they issue patches.”
Read More: Digital Transition Poses Key Payments Choices for Financial Institutions

Leaks in the Patch Pipeline
One of the gaps in apps is the patch process: Making sure the patches make it from the original developers to the developers in financial institutions who bolt together many programs into apps and then to the App Store or Google Play and finally to consumers. Ideally new downloads have been patched and are up to date and consumers are routinely allowing apps on their phones or tablets to be updated when they receive a notice that a patch is available.
Mackey likes to use the analogy of car manufacturing, where many components are subcontracted out and assembled at the factory to produce the car. Extending his analogy, patches are like recalls.
Banking apps have numerous functions that may require interfacing with other organizations and with multiple functions on the mobile device. Shooting a check, paying via Zelle or Venmo or PayPal and more all demand software that may initially come from the outside.
If financial institutions fail to pay attention to notices of security, performance or stability issues, he continues, that’s when data leaks can occur. If the end user of the app has disabled updating, they expose themselves to the risks. Mackey says he receives a half dozen updates every evening from all the apps he has on his mobile phone.
Sobering Thought:
Synopsys found in its overall analysis that 73% of vulnerabilities identified were disclosed two or more years ago. This means “developers simply aren’t considering the security of the open source components they used to build their apps.”
Again, if any link in the communication chain gets broken, then the fix doesn’t get made. “The longer a vulnerability remains unaddressed, the more likely it is to be exploited, and the more difficult it can become to make the fix,” the report states.
Read More: How Chase Bank is Tackling Top Digital & Mobile Challenges
Looking at Permissions that Apps Ask For
There are other vulnerabilities, such as connections between the app and the financial institution’s servers that may not be completely secure. A key one that the report looked at was permissions requested by legitimate apps to access functions or data within the device.
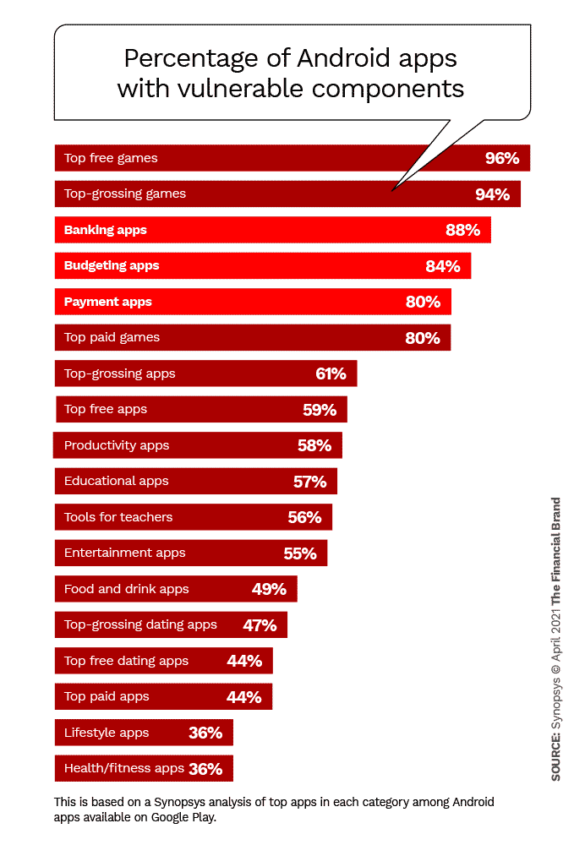
Financially related apps are especially high in requested permissions compared to other types of apps. Banking apps average 25 permissions, payment apps 25 as well, and budgeting apps 26 permissions, according to Synopsys’ analysis.
Responsibility is twofold, according to Synopsys. Developers need to be clear what permissions are being requested by the components they use to build their apps. And consumers need to be very aware of what permissions they are granting when apps ask them — and seriously consider whether they should agree.
“Some permissions are considered more sensitive,” says Mackey. “Having access to your phone or text messages, your camera and your location information are pretty sensitive sets of permissions that you don’t want to just grant to any application.”
“Permissions should align with what people expect about that application. Some banking permissions will involve more sensitive requests, things that wouldn’t make a whole lot of sense if you were just using the Yelp app.
— Tim Mackey, Synopsys
Mackey says consumers should be raising objections when too many permissions are being requested: “They should engage with their institution and say, ‘I tried to download your app and it asked for a boatload of stuff. That doesn’t make any sense to me. What gives?’ And it may turn out that the download that the end user had wasn’t actually the official app, but a fake that looked the same.”